Measure structure.
Prevent collapse.
ActProof is a structural diagnostics framework for autonomous systems. It is also a production-grade operating layer implemented in AI, enterprise and monitoring systems.
What is ActProof?
The Framework
Systems fail not because of output errors but because of hidden control cost. ActProof measures structural tension before collapse — quantifying how much effort a system spends on internal regulation instead of productive output.
The Systems
ActProof OS, CCC, and companion modules are production-grade systems built on this framework. They operate in AI safety, enterprise workforce management, and process monitoring — delivering real-time diagnostics without modifying underlying models or processes.
Core Metrics
Five diagnostic primitives that power every ActProof system.
Control Cost
The structural cost of steering a system toward its target. Measures how much regulatory effort is consumed internally — the higher the CC, the more fragile the system.
Latent Tension
Hidden stress gradient within the system. T rises when components compensate for each other silently — invisible to output metrics, but structurally dangerous.
Module Compensation Index
Detects when one module compensates for another's failure. High MCI means the system appears stable but is structurally dependent on a hidden workaround.
Flashover
The critical point where accumulated tension exceeds the system's capacity. Analogous to structural flashover — the moment before the system collapses under its own regulation cost.
Accumulator Φ
Global memory of accumulated control cost. Φ tracks how much structural debt the system has built over time. When Φ exceeds Φ_critical, flashover is triggered.
From Theory to System
Every framework concept has a direct implementation in production systems.
| Concept | Implemented As | System |
|---|---|---|
| Control Cost (CC) | CC_turn |
CCC |
| Latent Tension (T) | THS module | CCC |
| Module Compensation | MCI heatmap | CCC, ActProof OS |
| Flashover | System State Machine | All systems |
| Accumulator Φ | CC_global |
ActProof OS, CCC |
| Regime Classification | STEERABLE / RESILIENT / RIGID / CRITICAL | Diagnostic Engine |
Production Systems
Real infrastructure. Deployed, tested, operational.
CCC
Conversation Control Cascade
AI stabilization layer implemented as a thin wrapper around LLM systems. Does not modify weights, does not interfere with training, does not interpret user intent. Measures CC_turn, detects MCI between modules, monitors system fragility via T.
ActProof OS
Event-Sourced ERP Engine
Enterprise operating layer for workforce management, attendance tracking, and operational risk analysis. Every operation is an immutable event in an append-only log with deterministic rebuild guarantee.
- ✓ Employee & cost center management
- ✓ HMAC-signed QR attendance
- ✓ Bradford Factor risk analysis
- ✓ 9-phase cascading rebuild
UDM
Unified Diagnostic Model
Formal diagnostic core used by all ActProof systems. Defines state space (S), model space (M), compensation space (C), and accumulator memory (Φ). The mathematical layer from which CCC, OS and all modules derive their metric definitions.
Workforce Engine
Projection & Risk
Workforce projection engine with absence risk scoring (Bradford Factor), department-level tension detection, and automated monthly reporting. Identifies operational collapse risk before it becomes visible.
Process Monitor
Real-time SSE Stream
Real-time event broadcast via Server-Sent Events. Tenant-isolated streams, backlog replay from any sequence number, and daily timeline projection with cap guardrails. Deterministic rebuild verified by integration tests.
Telemetry & Guardrails
Limits & Alerts
Safety layer with configurable thresholds, severity truncation, cap guardrails (500 events/day/entity), and automated alerting. Ensures system stability under load without manual intervention.
AioP — Agent-to-Agent Contracts
Deterministic contract execution protocol. No LLM interpretation — pure structured actions with cryptographic proof. See the full flow below.
/contracts/{id}
Load Contract
Immutable, versioned contract with services, pricing, and constraints. Signed with contract_hash.
{
"contract_id": "3c3a2b6b-...",
"version": "1.0",
"status": "ACTIVE",
"issuer": { "name": "Salon XYZ" },
"currency": "PLN",
"price_unit": "MAJOR",
"contract_hash": "a7dbb1c1..."
}/sessions
Pin Session
Session pins contract_hash. TTL enforced. Agent locked to this version.
{
"session_id": "b684ed55-...",
"pinned_contract_hash": "a7dbb1c1...",
"expires_at": "+15 min"
}/execute
Execute Action
Server validates JSON Schema + constraints (lead time, working hours, service existence). Deterministic result.
{
"status": "ACCEPTED",
"execution_id": "51b4d1d6-...",
"proof_id": "52eebc49-...",
"result": {
"service_name": "Strzyżenie męskie",
"final_price": 60,
"currency": "PLN"
}
}/proofs/{id}
Verify Proof
Cryptographic proof: SHA-256 hash of canonical proof_body + HMAC server signature. Independently verifiable.
{
"proof_hash": "7093daa2...",
"server_signature": "q0xVk2Sq...",
"proof_body": { ... },
"✅ canonical(body) → SHA-256 = proof_hash"
}When the game was already lost — though no one saw it
A structural analysis of a Go game that shows how hidden tension works in any system.
What happened?
In 2016, a computer program played against one of the world's best Go players. At one point it made a move that surprised everyone. Commentators called it brilliant. But was it really "genius"? Or was it the moment when the system crossed a tension threshold?
Why was it surprising?
The move seemed illogical. Professional players said no human would play it. Probability estimates gave it less than 1 in 10,000 chance. Yet after that move, the entire game shifted. The opponent — a world champion — never recovered. Evaluations flipped. The game entered a completely different state.
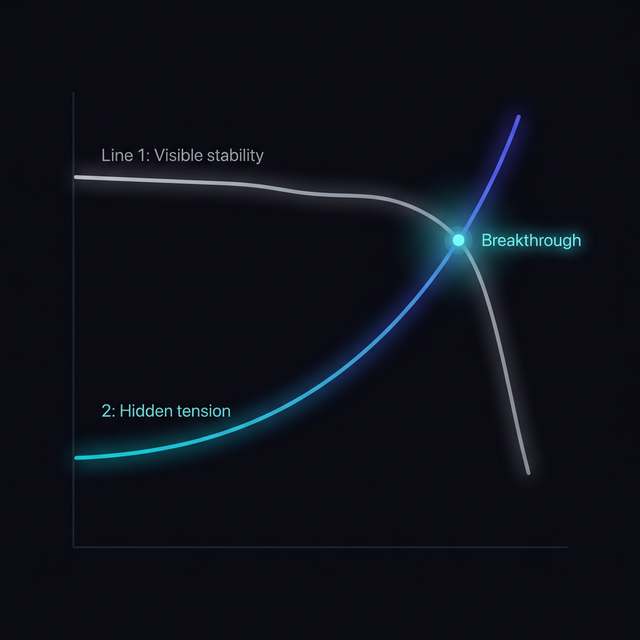
Visible stability stays flat while hidden tension grows — until the breakthrough point.
What was happening beneath the surface?
Imagine the game as a spring. Every move tightens it slightly. For a long time everything looks stable. The position seems balanced. Both players appear to have options. But the tension builds. Until at some point — the spring snaps to a new state.
In ActProof's language, we would call this a rise in control cost and latent tension. The system was spending more and more effort on internal regulation — while still appearing stable externally.
The moment of no return
After that move, the opponent had to play increasingly defensively. Every subsequent move required more effort to maintain balance. The position still looked "alive" — but its stability was already an illusion. The cost of holding it together exceeded what the system could sustain.
This is an example of what ActProof calls "flashover" — the moment when hidden tension exceeds the system's ability to stabilize. The collapse appears sudden, but structurally it was building for a long time.
What this says about systems
The same mechanism operates in AI systems, companies, and teams. For a long time everything looks fine. But the cost of maintaining stability grows. Until at some point the change becomes sudden and irreversible.
ActProof was built to detect this — before the moment arrives.
Example: AI System with CCC
A realistic deployment scenario showing how CCC prevents structural collapse in an LLM pipeline.
LLM with safety layer
Standard LLM pipeline deployed with content safety module. System appears stable in output metrics.
Alignment tax rises
Safety module increasingly overrides model output. edit_ratio climbs. CC_turn rises each conversation turn. Invisible to standard monitoring.
MCI detects compensation
CCC's MCI heatmap shows DG→SCE compensation pattern. One module is silently covering for another. T gradient rises.
CC_global accumulates
Accumulator Φ grows. THS (Temporal Horizon Scanner) detects escalation trend. System classified as RIGID.
Flashover prevented
Before Φ exceeds Φ_critical, Control Knobs adjust pipeline parameters. Regime shifts from RIGID to STEERABLE. Collapse avoided.
Integration & Deployment
Designed to fit existing infrastructure. No retraining, no vendor lock-in.
REST API and SDK available for integration. Full specification provided during technical onboarding.
Built for decision-makers
- Architecture diagrams with formal component boundaries
- API layer with telemetry input and dashboard output
- Defined deployment model (Docker, systemd, Caddy)
- Overhead below 5% — measured, not estimated
- 300+ integration tests with deterministic rebuild verification
- New category: structural diagnostics layer
- Cross-domain applicability: AI safety + enterprise + monitoring
- Proprietary metrics (CC, T, MCI) — difficult to replicate
- Formal mathematical model (UDM) as intellectual foundation
- Production-deployed, not conceptual
- SDK interface for custom integrations
- REST endpoints for diagnostics and telemetry
- Control Knobs API for runtime parameter adjustment
- Event-driven compatibility (SSE, webhooks)
- Middleware integration — zero model modification
Want to see
ActProof in action?
Get in touch — we'll schedule a demo and walk you through the architecture.